Detect authorization flaws, business logic vulnerabilities, and multi-tenant data leaks during development not in DAST or VAPT. Exploit validation proves it’s real. AI auto-fix generates patches in seconds.

Spotter brings DAST-level confidence to SAST-stage detection. Find vulnerabilities at source, prove they’re exploitable, and get the fix all before code review.
Every vulnerability is validated with automated proof-of-concept testing. Only genuinely exploitable issues are reported. 94% reduction in false positives.
AI generates context-aware remediation patches automatically. Get pull requests with fixes ready for review no manual coding required. Seconds, not hours.
Catch authorization flaws, business logic vulnerabilities, and multi-tenant data leaks at the SAST stage not weeks later in DAST or VAPT.
Learns your codebase patterns, maps data flows, understands business logic, and recognizes your framework conventions Rails, Django, Spring, Express.
Authorization bypass, IDOR, business logic flaws, multi-tenant data leaks, race conditions the vulnerability classes that cause today’s breaches.
Superior understanding of AI-produced code. Catches hallucinated auth checks, insecure patterns from Copilot, Claude Code, ChatGPT, and Cursor.
See the difference between traditional SAST and Spotter’s adaptive approach across every dimension that matters.
| Capability | Traditional SAST | DAST / VAPT | Spotter |
|---|---|---|---|
| False Positive Rate | 53% (industry avg) | 10–15% | <6% (94% reduction) |
| Authorization Flaw Detection | Pattern matching only | Manual testing | Context-aware + validated |
| Business Logic Vulnerabilities | Limited patterns | Manual analysis | Understands workflows & state |
| Multi-Tenant Data Leaks | Can’t understand tenancy | Limited coverage | Analyzes tenant isolation |
| Exploit Validation | No | Manual PoC | Automated PoC testing |
| Automated Fixes | No | No | AI-generated patches in PRs |
| AI-Generated Code Analysis | Same as human code | N/A | Specialized AI code analysis |
| Time to Fix | Hours per vulnerability | Hours per vulnerability | Seconds with auto-fix |
| Time to Results | Minutes (shallow) | 2–4 weeks | Minutes (deep) |
| Cost Per Finding | ~$1,000 | ~$600 | $0.05 |
Six steps from integration to continuous improvement. Deploy in minutes, start catching real vulnerabilities immediately.
Connect to your IDE or CI/CD pipeline. Works with GitHub, GitLab, Bitbucket, Jenkins. Deploy in minutes.
Adaptive engine analyzes your codebase structure, authorization patterns, and business logic. Maps your framework conventions.
Context-aware scanning finds authorization flaws, business logic vulnerabilities, and multi-tenant data leaks other tools miss.
Automated proof-of-exploit testing validates every finding. Only reports vulnerabilities that are actually exploitable. No false positives.
AI generates context-aware patches for every validated vulnerability. Creates pull requests ready for review. Fix in seconds.
Continuous learning adapts to your team’s patterns, reduces noise, and improves accuracy with every scan.
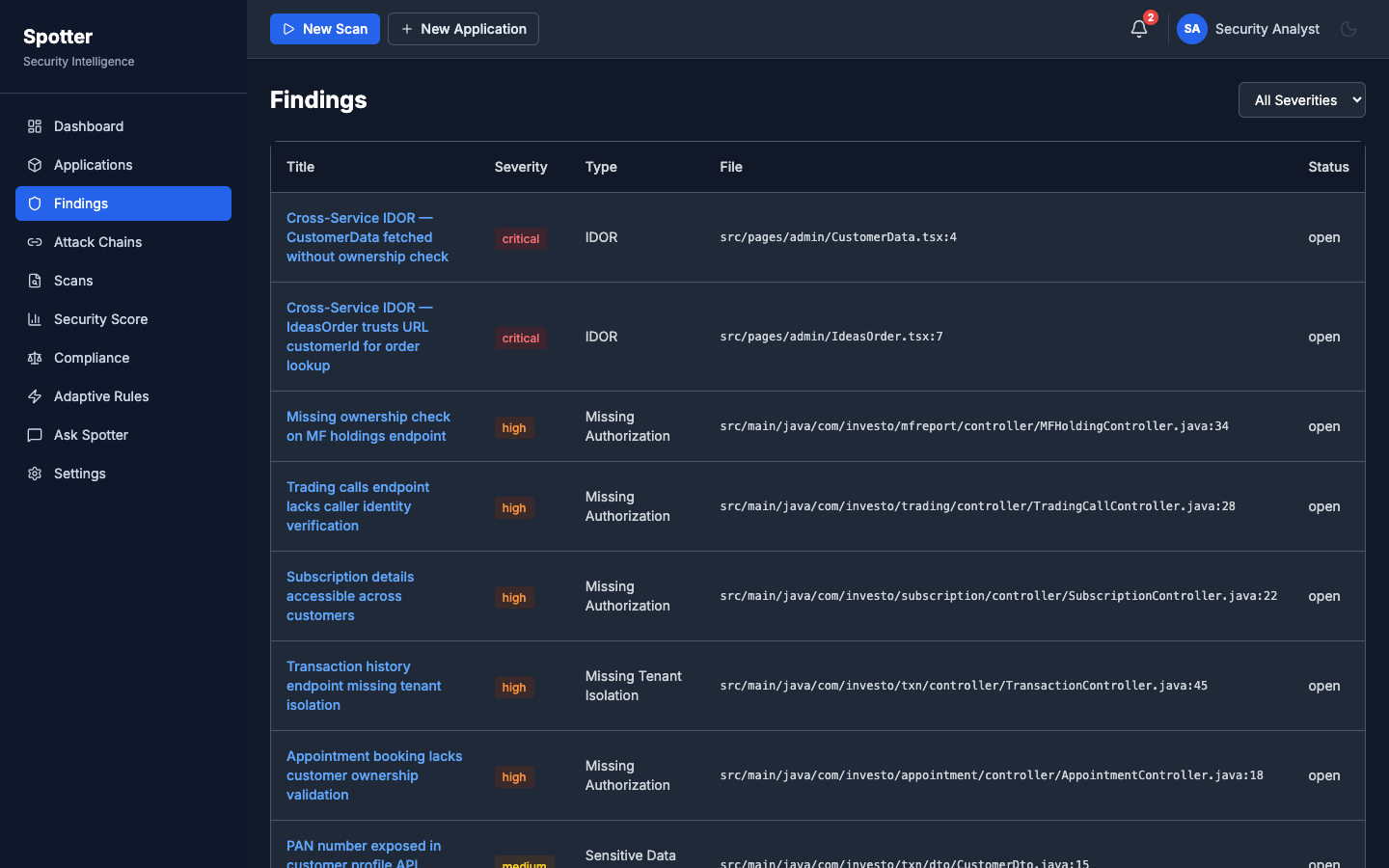
A real IDOR vulnerability discovered in a 28-service fintech platform in 10 minutes for $3.
A customer could change a URL parameter (/admin/customer/123 → /admin/customer/999) and access any other customer’s full financial profile portfolio, balances, PII.
Whether you’re a developer, security lead, or CISO Spotter solves your specific pain points.
Building multi-tenant SaaS? Your authorization logic is complex. Traditional SAST generates hundreds of false positives while missing critical tenant isolation flaws.
53% of SAST alerts are false positives. You spend weeks triaging noise while real authorization flaws only surface in VAPT too late, too expensive.
Business logic spans dozens of services and is your attack surface. Authorization vulnerabilities can’t be found with pattern matching alone.
Copilot, Claude Code, ChatGPT accelerate you but introduce hidden risks hallucinated APIs, missing context, subtle auth bypasses that traditional SAST can’t catch.
Join forward-thinking engineering teams shifting security left. See what your current tools are missing in 20 minutes.
Schedule a DemoFree demo scan on your codebase. No commitment required.
Real Vulnerabilities. Real Results.
Spotter catches the vulnerabilities that cause breaches not just the ones that fill reports.
“Spotter found 3 CRITICAL cross-service vulnerabilities that SonarQube, Semgrep, and Snyk all missed. In 10 minutes. For $3.”
“We were missing tenant isolation issues in code review. Spotter caught 12 cross-tenant data leaks before they reached staging.”